It probably isn’t a question you’ve put much thought to, but tell me: who do you think feels the greatest impact from card skimming schemes, where a payment card’s data is captured so a cybercriminal can make use of the card’s associated account? While it isn’t a good situation for anyone, some are impacted more than others.
SolutionOne Blog
WhatsApp is one of the world’s most popular messaging applications. With over 2 billion users, WhatsApp is known for its relative security, as it is one of the few messaging applications that offers end-to-end encryption. A modified version of WhatsApp, called YoWhatsApp, has been reportedly deploying malware.
Ransomware is one of the more dangerous threats out there today, and since it is so prominent and dangerous, it is a popular choice amongst hackers. To combat this threat, a community has formed around the cause, encouraging users to not pay the ransom by providing free malware removal tools for the most popular ransomware threats.
If you watch technology news, you might notice that there is one day out of every month that gets a lot of attention from the technology sector, and that day is what is called Patch Tuesday. This is the day each month when Microsoft issues all of their patches and security updates, and it’s important to know when this day falls each month—at least, for your IT team it is.
We’re not shy about sharing how important it is for a business to have comprehensive cybersecurity throughout its entire infrastructure. That’s why we wanted to share what some recent data has shown about the importance of having visibility into your infrastructure.
Spoiler alert: it’s really, really important.
At first glance, cybersecurity might seem incredibly complicated and difficult to understand, but even a baseline understanding of some of the principles of cybersecurity can go a long way toward protecting your business. Let’s discuss some of the common-sense ways you can keep your business secure, even if you don’t have an internal IT department to ask for help from.
How often do you get emails from individuals claiming to be working with a business who wants to do business with yours or sell you a product, completely unsolicited and even perhaps a bit suspicious? These types of messages can often land small businesses in hot water, as it only takes one phishing email landing in the wrong inbox at the wrong time to put your business in jeopardy.
This past year saw a dangerous 86% increase in the most dangerous types of malware out there, so we want to ask you an important question: are you ready to protect your business from the different types of threats you might encounter? We know a technology solution that might help this mission along, and we want to share it with you today: artificial intelligence.
It’s easy to use the terms “patches” and “updates” as if they mean the same thing, and they are often used interchangeably within the same context. However, understanding the difference between the two can make a world of difference in terms of how you approach implementing each of them. We’re here to clear things up a bit and help you better understand the patches and updates you deploy on a month-to-month basis.
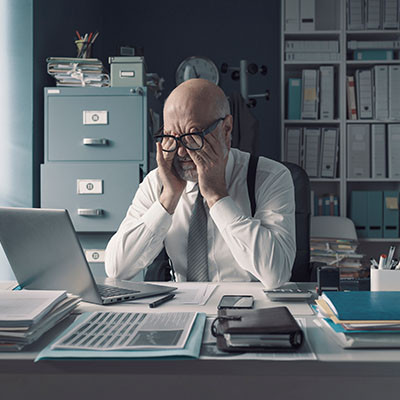
Chances are pretty good that, by this point, you’ve heard of burnout—maybe you’ve even suffered from it before yourself—but, just in case you’re a remarkably lucky human being, it’s the phenomenon where your employees become disengaged to the point where their performance suffers. While this isn’t good in any facet of your business, it can be especially damaging in terms of your security.
Insurance is a great asset, should you ever need it… including where your business technology is concerned. If you weren’t aware, there is a form of insurance—cyber insurance—that you can purchase in case your business suffers from a data breach.
Is this additional form of insurance worth the investment? Absolutely.
When we think about cybersecurity, we usually think about protecting our computers from viruses, right?
I’d imagine a few of our older readers remember a time when you would go to the store and buy antivirus software that came in a big brightly-colored box with a CD in it each year.
As you probably already know, things aren’t as simple anymore.
Anyone who has a mailbox or an email knows all about junk mail. We all receive Publisher’s Clearing House entries, calls about your car’s extended warranty, promotions for items and events that you swore that you discontinued by typing “STOP”, and just needless spam that you waste your time going through and deleting. We receive unsolicited messages every single day.
Mobile devices demand a special type of attention in order to ensure security. You want to ensure that your devices are protected as well as possible, but you also need to ensure that this does not come at the expense of your employees’ productivity or efficiency. We’ve put together a list of common security issues you might encounter when securing your mobile devices, as well as a couple of practices you can implement to work toward an adequate level of cybersecurity for your mobile infrastructure.
If you are a frequent reader of our blog, you know all about phishing scams. They are emails and messages sent that are designed to extort money and gain access to computers and networks for nefarious purposes. The popular IT support company Geek Squad, a subsidiary of Best Buy, is the latest company caught up in such a scam. Let’s take a look at how the scam works and how you can avoid becoming its next victim.
Your network security is of the utmost importance to your business for numerous, hopefully obvious reasons. However, there are a few errors that are easy enough to make that could easily be the proverbial monkey wrench in the works. Let’s go over what these network security faux pas look like, so you can resolve them more effectively (and don’t worry, we’ll discuss that, too).